
The Aflac Breach Was Preventable — Token’s Technology Proves It
Token, a revolutionary provider of secure, biometric identity protection solutions, announced that its technology is the industry’s only available solution that could have prevented the serious data breach that Aflac confirmed on June 20, 2025. The Alflac breach possibly exposed customers’ Social Security numbers, insurance claims, and personal health information and is considered to be the biggest breach in a growing wave of cyberattacks targeting the insurance industry.
This press release features multimedia. View the full release here: https://www.businesswire.com/news/home/20250623910197/en/
www.tokenring.com
“With billions in revenue and millions of customers, Aflac now joins a troubling list,” said Kevin Surace, Chair, Token. “Erie Insurance and Philadelphia Insurance Companies were also hit this month, with major IT disruptions affecting customer services.”
According to industry experts, sources close to the investigation say all signs point to Scattered Spider —a fast-moving, aggressive cybercrime group that’s quickly becoming a top threat. The breach method relies on (and expects) legacy multi-factor authentication (MFA) — where SMS codes can be intercepted or relayed, and users can be tricked into approving authenticator app prompts during real-time phishing. These methods are easily manipulated and no longer offer protection.
This type of hack requires little to no technical ability, and almost anyone who can create a simple spoofed webpage can execute this hack in minutes, leaving every company fully exposed today.
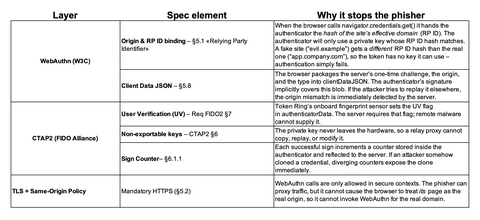
Token Ring and Token BioStick leverage a combination of biometric ID (fingerprint) and proximity (using encrypted Bluetooth) to the specific device logging in to the actual registered application. Token stores a unique private key per site, secured by fingerprint. During login, it signs a one-time challenge from the real site’s FIDO2 server, which verifies the signature and origin. If the origin doesn’t match, the login is rejected — blocking phishing and spoofing outright.
This stops real-time phishing because every credential is cryptographically locked to the exact web origin it was created for, and the authenticator will only sign a challenge that (a) comes from that origin and (b) is confirmed by a live fingerprint-match. A phisher can steal nothing re-usable and cannot trick the token into signing for the wrong site. If Aflac employees were using a Token product, the hack could not have occurred.
Why the “real-time relay” trick fails
|
1. |
|
User originally registered a Token device with the true site |
||
|
|
|
a. |
|
during the registration with the true site, public/private cryptographic key pair is negotiated which is required and validated during every subsequent passkey operation from that device to that site |
|
|
|
b. |
|
the serving site retains the public key which is used for further trusted communications with the private key on the device |
|
2. |
|
Hacker pushes a phishing email to the victim. |
||
|
3. |
|
Victim opens the phish page.
|
||
|
4. |
|
A sophisticated Phish page could potentially ask for Authentication for the true site not evil.example
|
||
|
5. |
|
Even if the Browser passes the true page name to the Token FIDO2 authenticator, the attacker's domain does not possess the cryptographic credentials for the true page to complete the authentication process with the private key on the device |
||
|
6. |
|
Token Device has no identity for the incorrectly cyphered request ⇒ authentication fails - technically doesn't occur |
||
|
If the attacker tries to be very clever and relay the legitimate site’s WebAuthn challenge through its proxy: |
||||
|
|
|
|||
Summary:
Because Token products store a negotiated key pair per site and will only release a signature when:
- The site matches the domain the user is really visiting, and the domain has the secret key pair which matches the initial device registration, and
- The fingerprint sensor verifies the legitimate user.
A remote adversary has no path to “spoof the key” or “forward the signature” the way they can with OTP codes or push-approval apps. Implemented correctly, FIDO2 offers true phishing-resistant MFA — and that’s what makes biometric Token products orders of magnitude safer than legacy MFA.
The fastest, most effective way to lock down your data and networks is to roll out Token Ring or Token BioStick across your workforce. Even if an employee falls for a phishing email, hackers still hit a dead end. Why? Because legacy MFA — like SMS codes and authenticator apps — is laughably easy to bypass. Hackers relay codes, spoof app prompts, and trick users every day.
But Token’s biometric FIDO2 authentication and proximity controls make that impossible. Credentials never leave the device, can’t be replayed, and only work with a live fingerprint match and the right domain next to the actual device logging in. It’s the difference between a padlock and a vault.
About Token
In a world of stolen identities and compromised user credentials, Token is changing the way our customers secure their organizations by providing passwordless, biometric, multifactor authentication. We deliver the next generation of multifactor authentication that is invulnerable to social engineering, malware, and tampering for organizations where breaches, data loss, and ransomware must be prevented. To learn more, visit www.tokenring.com.
View source version on businesswire.com: https://www.businesswire.com/news/home/20250623910197/en/
Distribution channels:
Legal Disclaimer:
EIN Presswire provides this news content "as is" without warranty of any kind. We do not accept any responsibility or liability for the accuracy, content, images, videos, licenses, completeness, legality, or reliability of the information contained in this article. If you have any complaints or copyright issues related to this article, kindly contact the author above.
Submit your press release